UPDATE: This post has some great ideas, however if you’d like an easier way to accomplish this with Item-level targeting navigate to this new post.
This post I’m going to detour from the usual Home Theatre write up. I still have more Home Theatre to go through, however I though I would give this topic a little attention. So recently I embarked on locking down my companies computer systems and what better way to do it with than Group Policy. Well I ran into a little problem when I tried to assign a single user as a local administrator on a single domain computer, it seemed impossible to accomplish with Restricted Groups as they encompass the entire OU no one single computer.
I searched the dark recesses of the internet and I thought I had found a link on social.technet, but as it turned out this did not allow me to do all the work remotely and I had to add additional groups to the computers. Then further looking over what Alan Burchill wrote I concluded that with his implication of the policy local administrators would be able to add other network users as local administrators, this did not work for me. I want to rule with an Iron Fist!!!
Either way what Allan had set out for me in black and white was a very good start and it really helped . Some of the comments in the post also shone some light on the behaviour of the Policy. You can find Allan’s blog post in regards to this here: http://www.grouppolicy.biz/2010/01/how-to-use-group-policy-preferences-to-secure-local-administrator-groups/.
What’s nice about this method is that it will also clean up your policy each time it gets updated or anyone logs on to the computers in the OU. So if anyone adds another admin user to the group they will be removed. Also if you have some old administrators on PCs that were added manually in the past and have since left this will remove them.
Well let’s get on with it then, shall we.
My environment consists of Server 2008 R2 and Windows 7 machines.
I run my policy editor on my local machine, however I recommend you run it off your server since you can run gpupdate /force from there as it propagates faster this way.
1. Start the policy editor on your server by going to Start > Run > gpmc.msc
Create a new policy under the OU in which you have your domain computers.
 2. Edit the policy and navigate to Local Users and Groups, Computer Configuration > Preferences > Control Panel Settings > Local Users and Groups.
2. Edit the policy and navigate to Local Users and Groups, Computer Configuration > Preferences > Control Panel Settings > Local Users and Groups.
3. Right click in the right pane of the window and select New > Local Group, you will be prompted with a New Local Group Policy window.
4. The Action heading should be set to Update, from the Group name drop down list select “Administrators (built-in)”, check off “Delete all member users” and “Delete all member groups”. Only use these options on the first Order policy as these are the options used to clear any previously assigned users and groups to the Local Administrators group.
 5. Next we will add a single member to this new Local Admin policy. Click Add and you will be prompted with Local Group Member window, in the Name: section type in “BuiltIn\Administrator” this adds the Administrator account present on all machines to the Administrators group. For Action: select Add to this group.
5. Next we will add a single member to this new Local Admin policy. Click Add and you will be prompted with Local Group Member window, in the Name: section type in “BuiltIn\Administrator” this adds the Administrator account present on all machines to the Administrators group. For Action: select Add to this group.
6. Your Local Group Properties window should look like the following image. If yours looks the same go ahead and click OK.
7. This will take you back to the Group Policy Management Editor and you will have one policy with Order 1. The order is the order in which these policies get applied in. Since we’ll be adding more policies you may want to rename this policy in the Editor to something more descriptive like “Built in Local Admin”, highlight the policy and press F2 to do so.
In Allan’s blog he groups the assignment of the Built in Admin account and Domain Administrators group in one Local Group. What I have found to be the case is that if you have more than one member that is to be added to the Local Group and one of these members does not exists or the spelling is incorrect the Local Group policy will stop processing as soon as it encounters and error and refrain from processing any further Member assignments. As a good practice try and assign one member per Order.
8. Let’s create a new policy. This time we will add the Domain Admins group as Administrators to all the OU computers. Follow steps 3 & 4 again, with one exception, do not check off “Delete all member users” and “Delete all member groups” leave these unchecked otherwise when this policy is processed it will remove the previous members from policy Order 1 (Built in Local Admin).
9. When adding the member as in step 5, click in the Name: field and hit F3. You will be prompted with a Select a Variable window, select “DomainName” and make sure Resolve Variable is checked off then proceed and click Select. This will populate the Name field in the Group Member window add “\Domain Admins” to this so you have “%DomainName%\Domain Admins” in the Name field and click OK.
Your new policy should look something like the following image. You may not have a Domain Admins group on your domain, and if that is the case substitute the name of the group to the one that matches up with your domain administrators group. Now you should have two groups, go ahead and rename the second one as well. I renamed mine to Domain Admins.
10. In my 3rd order policy, since by default all local Administrator accounts are disabled, I ended up adding a local user account named “User” to all computers in the OU. Right click and select New User. It’s very similar to creating a new user on the domain.
11. In my 4th order policy I assign the User account to the Administrators (built-in) group. The only difference between this step and step 9 is instead of using the %DomainName% variable I’m using the %ComputerName% variable. Also to note you don’t need to hit F3 to select the variable you can type the information in manually ie. “%ComputerName%\User”. It should look like the following image. Click ok and rename the policy.
12. Now this is where the magic happens and we create an individualized local admin policy for a single computer. Before we create the policy we need to rename the Administrator group on each computer to something unique, after pondering this for a while I came up with the following solution. Create a new Local Group policy. Action: Update, Group Name: Administrators (built-in), Rename to: %ComputerName%.ADMIN. Do not Add any members leave this portion blank and click OK. Rename the policy if you would like.
The key here is the %ComputerName%.ADMIN, each computer will rename the Administrators group locally to something unique to that computer in this case it will use it’s name. For example a computer named DMCL-00203 will rename the local admin group to DMCL-00203.ADMIN. As seen below.
Once you have this in place you are able to add individual local administrators by creating new Local Group policies with higher orders than the policy which renames the local admin group.
13. To add a local administrator to computer DMCL-00203 create a new Local Group policy, Action: Update, Group name: DMCL-00203.ADMIN add a member using %DomainName%\UserId, UserID being a valid domain account.

You can add more member accounts to this policy just know that if it errors out or the account is invalid there is a possibility that the policy will not be applied to the computer. That is it, now you should have 6 policies in place depending on how many computers need local admin users. The order of the policies are important, for example you can not assign a local user to the admin group in order 6 if the user account gets created in order 7. Keep this in mind when designing your policy.

IMPORTANT UPDATE: So it seems the Active Directory likes to show all the computer admin groups created with in the policy on one single computer (see below). However that does not mean that the users in these groups have admin access to all computers on the network, having tested this they only have access to the computer they are assigned to. This is purely aesthetic.
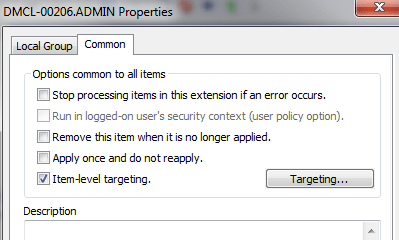
 In order to avoid this purely asthetic replication to other computers except the target machine use “Item-Level Targeting”, it is available under the common tab. So at the end of step 13. click the common tab, and check item level targeting and click the Targeting button. Then in the Targeting Editor select New Item and Computer Name, then Type in the computer name or look it up in the Domain using the … button.
In order to avoid this purely asthetic replication to other computers except the target machine use “Item-Level Targeting”, it is available under the common tab. So at the end of step 13. click the common tab, and check item level targeting and click the Targeting button. Then in the Targeting Editor select New Item and Computer Name, then Type in the computer name or look it up in the Domain using the … button.










What if two computers in the enterprise have the same name?
I tried to add user which logs on to the computer by typing %DomainName%\%Username% – why it didn’t work?
What if another user loggs on? I suppose that it will be also added to the %ComputerName%.ADMIN group – can it be done in the way that only the first user (which joined computer to the domain) can be added to this ‘%ComputerName%.ADMIN’ group?
You should not have two computers on an enterprise network with the same name, this is bad practice and can cause conflicts.
Each computer should have a unique identifier/name.
You have to note that everything is done in Policy. Nothing is changed on the computer side.
There are several steps involved in creating this policy for each step you need to create a new Local Group.
Each step will involve creating a new Local Group by right clicking, selecting – New – User Group.
Each time you will be Updating the Administrators (built-in) group, except for step 4.
All these below steps are performed in you Group Policy under, Computer Configuration – Preferences – Control Panel Settings – Local Users and Groups.
1. You need to add any local accounts to the Administrators (built-in) group.
All computers have the "Administrator" account, so add a new Local Group, set action to Update, Group name is Administrators (built-in), and Members will be %ComputerName%\AdministratorOn my domain I named this new Local Group “Local Administrator account”
2. You need to add any Domain Admin accounts to the Administrators (built-in) group.
Add yet another new Local Group call it . Here you add a domain user, set action to Update, Group name is Administrators (built-in), and Members will be %DomainName%\zawisza , zawisza being a user name of a Domain Admin.On my domain I named this new Local Group “Domain Admins”
3. Then you rename the Administrators (built-in) group.
Add another new Local Group, action is Update, group name Administrators (built-in), Rename to %ComputerName%.ADMIN, there are no members in this group.On my domain I named this new Local Group “Rename Administrators Group”
4. Here is where you create a computer specific ADMIN group. This is where you grant an individual user Admin rights on a specific computer.
In this example let's say you have a computer on the domain called "MojKomputer". Create a new Local Group, Action is set to Update, group name MojKomputer.ADMIN, Members %DomainName%\zawisza.Name this Local Group something like “Administrator dla MojKomputer” 😉
If you only want to add one user as an administrator to all the computers on the Domain, do only step 2 of the above, ignore all the other steps.
Hello, I’m trying to get it working in my domain, without success 😦 Domain Windows 2008, client Windows 7 Pro SP1 “Remote Desktop Users (built-in)” ; “delete all members users” and “delete all members groups” selected; Members action ADD: MyDomainName\GlobalRDPUsers In the window under Members section I see: Name Action SID MyDomainName\GlobalRDPUsers ADD S-1-5-21-20….. and this policy is not removing any other accounts in “Remote Desktop Users” local group nor adding that MyDomainName\GlobalRDPUsers In GPO Result I see that this policy had been applied with success but apparantly result is wrong.
OK, problem solved. Selecting from the drop down list “Administrators (built-in)” caused in my case that the new local group is created with this name and all actions are performed on that group instead of “real” local Administrators group. So in my case I have had to put in “Group Name” field the name “Administrators” instead od “Administrators (built-in)”
‘If you only want to add one user as an administrator to all the computers on the Domain, do only step 2 of the above, ignore all the other steps.” – I don’t know if I got it right, but I don’t want to have one user who would be administrator on every computer on the Domain. I wan to have each user to be administrator only on one, specified computer and nowhere else. So for example You bind the user only to the computer he joined to the domain and then You make him an administrator there and nowhere else. How to do that?
You should always assign the built in “Administrator” account and the “Domain Administrators” group to the local Admin computer groups.
Then Start with Step 12 in the post and continue on. This is where you assign individual users as admins to the domain. Note that these policies override the admin settings on all computers and replace them on the domain. Unless this policy applies to a specific OU.
Will the local admin rights stay operational when the user logs on later with cached credentials not being connected on the network?
Absolutely, the OS will cache all the domain credentials and group policy locally.
I already know how to do this part, however I need some assistance, I have created a GPO that specifies/mandates a BGinfo wallpaper and a custom ssText3d Screensaver, however local users are not allowed to be local admins of their machines for security reasons. i know how to add Domain users or check the box for add current user to get them into the built in Administrators, and on my test machines this allows the GPO to apply correctly, what i can’t get (probably something easy) is how do i make it remove that group or user AFTER the GPO applies? Do i need to another GPO configured to remove them and change the order in which the GPO’s apply? or just do another “add” within the same GPO to Remove current user/group? if so what order should they be in?
Thank You,
After this has applied to the computer, you would need to delete the existing policy, and create a new policy to remove the users or groups permissions. Mind you I don’t understand why you can’t use a domain admin account to push the wallpaper to all the computers.
Have a look at this blog post: http://dipanmpatel.com/2012/09/24/deploying-wallpaper-with-bginfo/
Hello There. I found your blog using msn. This is a really well written article. Ill make sure to bookmark it and return to read more of your useful information. Thanks for the post. I will definitely return. ebedafkekbeg
But a smiling visitor here to share the love , btw outstanding layout. dckccacdfffb
Hi Nerd,
I’m new to GPO though with years in the IT as to Linux/Network.
I’m stuck at the first step
”
1. Start the policy editor on your server by going to Start > Run > gpedit.msc
Create a new policy under the OU in which you have your domain computers.
”
Honestly by following this very first step I don’t see the way to locate an OU within gpedit.msc. A program that allows me to see the policies at the domain level and also the structure is te Group Policy Managemtn Console (gpmc.msc).
Where I’m wrong at?
Cheers
Thanks for catching that, and you’re right gpedit is just a policy editor. The management console is gpmc.msc.
I’ll fix it, thanks for that again.
Please check out the new post that accomplishes this with a lot more ease. https://nerddrivel.wordpress.com/2014/07/24/item-level-targeting-use-gpo-to-set-user-as-a-local-administrator-on-a-single-computer/
This is the right site for anybody who really wants to find
out about this topic. You realize a whole lot its almost hard to argue with you (not
that I really would want to…HaHa). You certainly put a brand new spin on a subject which has been discussed for decades.
Great stuff, just wonderful!
local admin on just one machine
I wrote a script which runs as a computer policy with administrative rights on the local workstation. It checks the last logged on user’s Description in AD which a Domain Admin can set from “Active directory Users and Computers”, if it contains the workstation name, the script adds the user to local admin group, if the workstation name is not in the user’s Description, it removes the user from the local admin group. A Description can include more than one computer name, like this:
The user’s Description: “Local Admin on WKST-E445R and WKST-VM398”
So to make someone a local admin on just one machine, I just have to add this computer’s name to the user’s Description in AD and ask user to reboot, and removing the computer’s name removes the local admin rights.
Isn’t that the neatest solution ever? 🙂
Here is the script:
@if “%debug%” neq “%username%” echo off
set ver=MakeLocalAdmin.cmd henrik@c o m m o r e.se 20150423
:: Adds last logged on domain user to local Administrators group if run by computer GPO with Administrative rights and the user’s Comment contains Computername
set log=nul
:: or set log=c:\logs\MakeLocalAdmins.txt
:: Check who was last logged on user
FOR /F “tokens=3 delims= ” %%G in (‘reg query “hklm\SOFTWARE\Microsoft\Windows\CurrentVersion\Authentication\LogonUI” /v LastLoggedOnUser’) DO (
set DomainAndUserName=%%G)
:: Remove the spaces
set DomainAndUserName=%DomainAndUserName: =%
:: Get only username part
set LastLoggedOnUserName=%DomainAndUserName:*\=%
:: Check OS language, so we can adapt to localized name of Admin group and Comment
FOR /F “tokens=3 delims= ” %%G in (‘reg query “hklm\system\controlset001\control\nls\language” /v Installlanguage’) DO (
set Language=%%G)
echo %date% %Time% ; %0 ; %computername%; %LastLoggedOnUserName%; %DomainAndUserName%, %Language% >> %log%
goto %Language%
:: Add any langauage specific part below, but if an unknown install language is found,
:: an error ‘label not found’ should mean script terminates, but anyway make sure it terminates.
goto end
:0409
:: English
net user /domain %LastLoggedOnUserName% | find “Comment ” | find “%computername%” >> %log%
set NoLocalAdmin=%errorlevel%
if %NoLocalAdmin% equ 0 net localgroup Administrators /add “%DomainAndUserName%” >> %log%
if %NoLocalAdmin% equ 1 net localgroup Administrators /del “%DomainAndUserName%” >> %log%
goto end
:041D
:: Swedish
:: †„” åäö (Swedish char’s)
net user /domain %LastLoggedOnUserName% | find “Kommentar ” | find “%computername%” >> %log%
set NoLocalAdmin=%errorlevel%
if %NoLocalAdmin% equ 0 net localgroup Administrat”rer /add “%DomainAndUserName%” >> %log%
if %NoLocalAdmin% equ 1 net localgroup Administrat”rer /del “%DomainAndUserName%” >> %log%
goto end
:end
Thanks for that. That is pretty cool.
I have since revised this and Updated it with a better way to accomplish it via GPO.
The post is about 1/3 of the length of this. It’s more efficient and easier to understand.
https://nerddrivel.com/2014/07/24/item-level-targeting-use-gpo-to-set-user-as-a-local-administrator-on-a-single-computer/
Muchas gracias. ?Como puedo iniciar sesion?
Sheer genius Loyd!! Much simpler approach to add a single user to the local admins group without clearing out the current users in the group than I have seen in any other post online. This worked like a charm for me on the first try.
I’m sorry to break this to you but computers on a domain should always have a unique identifier.
Computers on any one network for that matter.
I’m really surprised you are not getting DNS and DHCP conflicts.
I suggest you rename one of the computers and try again.
Thanks for the good writeup. It in truth used to be a amusement account it.
Look complex to more brought agreeable from you!
By the way, how can we communicate?
We need to figure out the solutions to restrict access to local admin groups based on the Group member ships.
Scenario – Say we have User1 and he needs local admin access on Specific Server say Server1, and we have a Group called Server.admin. when we make user1 member of Server.admin group he should get local admin on Server1. and
similar way we have User2 and he needs local admin access on other Server say Server2. and we make user2 member of same Server.admin group he should get local admin access on Server2.
This we are figuring out to achieve with Variables %Computername%. How to achieve the above requirement with Variables %Comptername% or any other methods.
Don’t use Groups, it’s inefficient and there would be extra steps involved in this.
Also your policies will look like a mess and you’ll have duplicate GPO’s
Just use a single policy and inside said policy under User – Preferences – Control Panel Settings – Local Users and Groups, add Administrators (built in) and do item level targeting.
If you must use groups then you have to use Security Filtering, remove Authenticated Users and add your group.
Then you either use WMI Filtering or Item Level Targeting inside the policy.
Regarding the performance about this method, for example, I have a lot of computers, lets say 100 Computers and each user should be a local administrator of their own computers. To elaborate:
User1 will be a Local Administrator of Computer 1 but not Computer 2 because User 2 is the only Local Administrator of that computer.
If I’m going to add this 100 Users in each of those 100 Computers using ITL to have a cleaner look of Local Users and Groups of each computer. Basically, I’m only going to have 1 GPO but contains 100 Users and 100 Computers. How is gonna affect the logon or startup of each computers that is affected by this GPO?
I would suggest following the link at the top of the page, this is the old method.
While this works it will flood your domain with the policy.
The newer method or revision does not and does not impact log in performance.
https://nerddrivel.com/2014/07/24/item-level-targeting-use-gpo-to-set-user-as-a-local-administrator-on-a-single-computer/